IoT Solutions for Every Application
Our Device Range
Connect more with our portfolio of deployment-ready IoT asset tracking and sensor monitoring hardware.
Discover what’s happening at Digital Matter
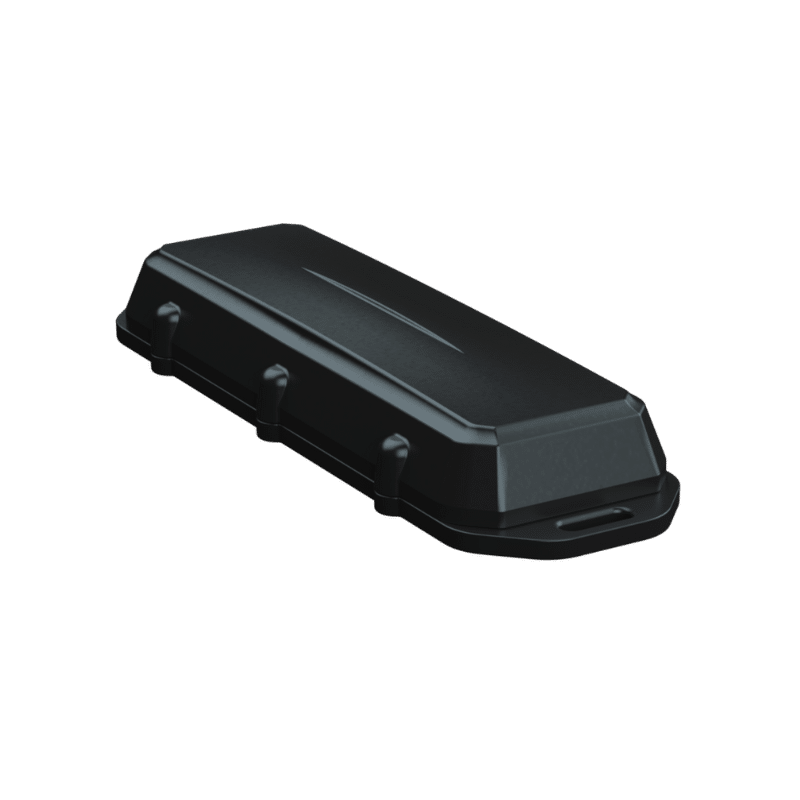
New Barra Device Family Enables Lowest-Cost IoT Asset Tracking at Scale
The Barra is our new low-cost, low-power device range that enables affordable an...
Oyster Edge Receives 2022 Asset Tracking Award
Oyster Edge Battery-Powered IoT Asset Tracker and Bluetooth® Gateway Honored fo...
Digital Matter Named Global IoT Innovation Vendor of the Year
We are thrilled to announce we were selected as the recipient of the “Global I...
Cellular IoT in Asset Tracking
Cellular IoT in the age of 5G, the difference between LTE-M and NB-IoT Networks,...
Roaming on LTE-M and NB-IoT Networks
Cellular IoT roaming on LTE-M/NB-IoT enables new asset tracking applications in ...
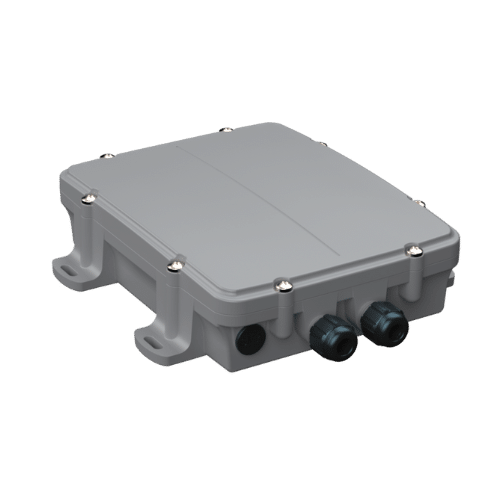
New Range of ‘Global-Ready’ Devices Feature 4G Cat 1bis with 2G Fallback
We're excited to announce the expansion of our battery-powered IoT asset trackin...
Let’s Get Started
Submit the form below to get in touch with a Digital Matter representative from your region.
Looking for support? Check out our knowledge base.
Information on becoming a Digital Matter Partner.
Information on pricing, availability, and proof of concept.
Guidance on selecting the right products for your application.